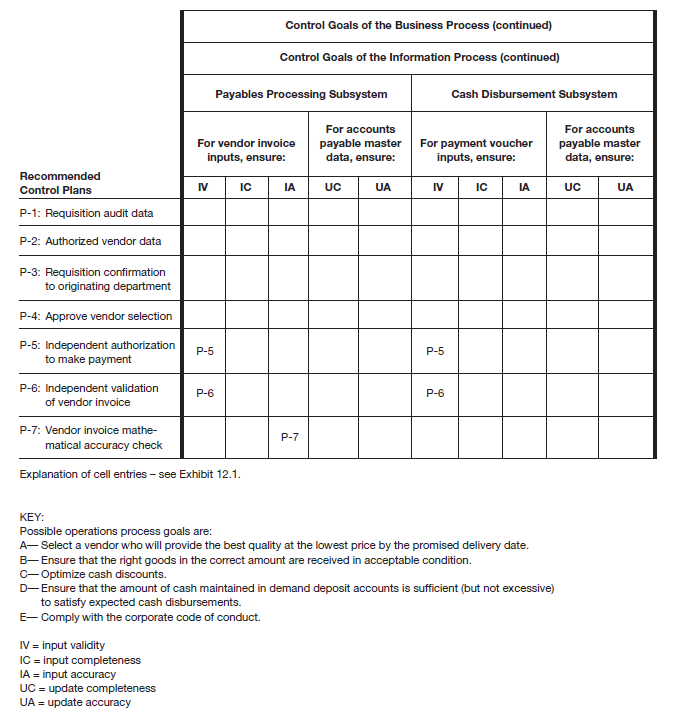
The following control-goal categories are presented in the matrix. Those for the operations process are:
- Effectiveness of operations relative to four example operations process goals. The first goal, mentioned earlier, might be to select a vendor who will provide the bestquality at the lowest price by the promised delivery date. When goods arriving at the receiving department are inspected, counted, and compared to the vendor packing slip, the receiving clerk is helping to achieve a second operations process goal: to ensure that the right goods in the correct amount are received in acceptablecondition. To help achieve a third operations process goal, to optimize cash discounts, the responsibility for ensuring savings through cash discounts includes (1) seeing that proper cash discount terms are incorporated in the order, (2) securing invoices promptly from vendors, (3) processing invoices promptly and getting them to the disbursing office within the discount period, and (4) when unavoidable delays are encountered because of some fault of the seller, making sure that the discount privilege is not waived and that the vendor is notified to this effect.

|
P-1: Requisition audit data. Purchase requisition input completeness: After all necessary approvals have been made, a copy of the requisition is automatically added to the audit data. This control plan ensures that a complete record is maintained of all requisition activity. P-2: Authorized vendor data. Select an appropriate vendor: Buyers in the purchasing department start the vendor selection process by first consulting the vendor master data, which contain only those vendors with whom the company is authorized to do business. The screening of vendors that preceded their being added to the “authorized” data should help ensure selection of a vendor who will provide the best quality atthe lowest price by the promised delivery date. Compliance with corporate code of conduct: Screening of vendors helps to ensure that company employees do not have financial interests in a vendor that would jeopardize their ability to be impartial in selecting a vendor with whom to place an order. Efficient employment of resources: People resources are used efficiently because time is not wasted in searching for vendors who might not supply the required goods or services. Purchase requisition input validity: The blanket approval accorded to vendors who are placed on the authorized vendor list also helps ensure the validity of purchase orders issued. P-3: Requisition confirmation to originating department. Purchase requisition input completeness: Once the purchase order has been signed and released by the purchasing manager, a confirmation of the requisition is sent to the requisitioner. Should the confirmation not be received in a timely manner, the requester follows up to see that the request is processed. P-4: Approve vendor selection. Select an appropriate vendor: After the purchase order is checked against the requisition details, it is approved by the purchasing manager—by adding his approval code to the purchase order record. The manager’s approval includes the vendor chosen by the buyer. Compliance with corporate code of conduct: This control plan could flag situations in which certain vendors appear to be favored in the vendor-selection process. Purchase requisition input validity: Approval by the purchasing manager helps to ensure validity of the purchase order. P-5: Independent authorization to make payment. Security of resources: Because cash cannot be expended in the absence of a validated, open vendor invoice, security over the cash asset is also enhanced. Vendor invoice and payment voucher input validity: Records in the open purchase order master data were created by personnel in the purchasing department. These data are the equivalent of hard copy purchase orders sent to the accounts payable department. Therefore, the data give independent authorization to the accounts payable system to approve vendor invoices for payment. The validity of both vendor invoices and subsequent payment vouchers is thereby ensured. P-6: Independent validation of vendor invoice. Security of resources: Because cash cannot be expended in the absence of a validated, open vendor invoice, security over the cash asset is also enhanced. Vendor invoice and payment voucher input validity: The computerized accounts payable application, which is separate from the departments that authorized the purchase and that recorded the receipt of the goods or services, actually performs the validation of the vendor invoice. Therefore, validity of both the invoice and resulting payment voucher is ensured. P-7: Vendor invoice mathematical accuracy check. Vendor invoice input accuracy: The accounts payable system matches invoice items, quantities, prices, and terms to comparable data on the purchase order and receiving report data. Because this process is computerized, we assume that the program also checks the invoice for mathematical accuracy (extensions, footings, discount calculations, etc.). |
Most cash managers attempt to optimize cash balances to help achieve a fourth operations process goal: to ensure that the amount of cash maintained in demand deposit accounts is sufficient (but not excessive) to satisfy expected cash disbursements. To accomplish this goal, many banks offer to their commercial customers a cash management service by which the bank transfers from the customer’s money market or other investment account into its checking account the exact amount needed to cover the checks that clear each day.
- Effectiveness of operations in respect to complying with the organization’s code of conduct concerning conflicts of interest, accepting illegal or improper payments, and like matters. Recall from IT Governance: The Management and Control of Information Technology and Information Integrity that one of the three categories of control objectives is compliance with applicable laws, regulations, and contractual agreements. For each process to which it applies, we have elected to include COSO’s “compliance” objective under our operations goals.
- Efficiency of the purchasing, receiving, payables, and cash disbursement processes.
- Resource security; note that the resources include assets, cash, inventory, and the information resources represented by the purchase order and accounts payable master data.
Controls for the information system are:
- Input validity (IV) of input events1
- Input completeness (IC) and input accuracy (IA)
- Update completeness (UC) and update accuracy (UA)
Input validity for each input event type can be summarized as follows:
- Purchase requisitions. Those that have been properly approved and that utilize existing (real) and approved vendors.
- Vendor packing slips. Those that are supported by authorized purchase orders and that represent existing (real) receipts of goods and services.
- Vendor invoices. Those that bill the company for goods that were actually ordered and actually received (i.e., the invoices are supported by proper purchase orders and receiving reports).
- Payment vouchers. Those that are documented by validated, unpaid vendor invoices. Note that in this case, part of ensuring validity is to prevent paying for an item twice.
|
Review Question What are four operations process goals of the PtoP process? Provide an example illustrating each goal. |
- 7316 reads